As businesses embrace digital transformation, many are adopting multi-cloud environments to leverage the unique advantages of different cloud providers. While this approach offers flexibility, scalability, and resilience, it also introduces significant security challenges. In this blog, we explore the best practices to secure multi-cloud environments, ensuring robust protection against evolving cyber threats.
What is a Multi-Cloud Environment?
A multi-cloud environment involves using services from multiple cloud providers, such as AWS, Microsoft Azure, and Google Cloud Platform (GCP). This approach enables organizations to avoid vendor lock-in, optimize costs, and utilize the best features of each provider. However, managing security across diverse platforms requires careful planning and execution.
Challenges of Securing Multi-Cloud Environments
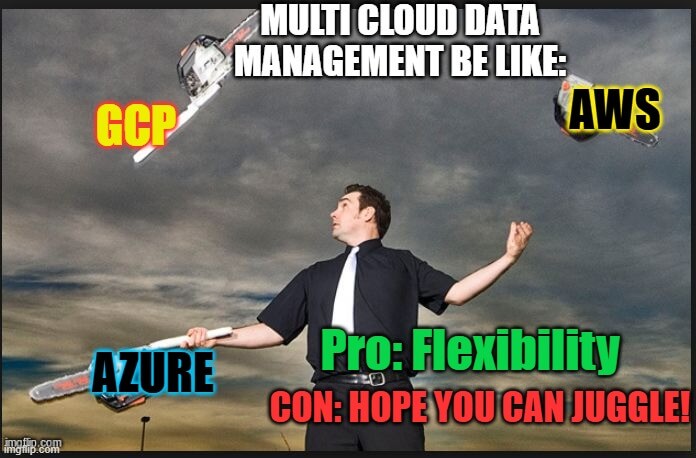
Before diving into best practices, it’s essential to understand the unique security challenges in multi-cloud setups:
Inconsistent Security Policies: Each cloud provider has distinct security configurations, making it challenging to implement a unified security policy.
Increased Attack Surface: Multiple cloud environments expand the potential entry points for cyber threats.
Complexity in Monitoring: Managing logs and security alerts across different platforms can be overwhelming.
Compliance Risks: Ensuring compliance with industry regulations like GDPR or HIPAA is more complicated when data spans multiple providers.
Lack of Visibility: Without proper tools, gaining a comprehensive view of security events across clouds is difficult.
Best Practices for Securing Multi-Cloud Environments

To address these challenges, organizations must adopt a strategic approach to cloud security. Here are the top best practices:
1. Establish a Centralized Security Policy
A unified security policy ensures consistency across all cloud platforms. Define clear guidelines for:
Access control
Data encryption
Security monitoring
Incident response
Use a Cloud Security Posture Management (CSPM) tool to automate policy enforcement across providers.
2. Implement Identity and Access Management (IAM)
IAM is critical in multi-cloud environments to prevent unauthorized access. Key steps include:
Use Single Sign-On (SSO): Simplify user authentication with a centralized SSO solution.
Adopt the Principle of Least Privilege: Restrict access based on roles and responsibilities.
Enable Multi-Factor Authentication (MFA): Add an extra layer of security for all accounts.
3. Leverage Encryption for Data Protection
Data security is paramount in multi-cloud environments. Protect sensitive data by:
Encrypting data at rest and in transit using strong encryption standards.
Managing encryption keys securely with a dedicated Key Management Service (KMS).
Regularly auditing encryption practices to ensure compliance.
4. Utilize Centralized Monitoring and Logging
Visibility is crucial for detecting and responding to threats. Implement:
Centralized Log Management: Aggregate logs from all cloud providers into a single platform for analysis.
Security Information and Event Management (SIEM): Use SIEM tools to monitor and correlate security events.
Cloud-Native Monitoring Tools: Leverage built-in tools like AWS CloudTrail, Azure Monitor, and GCP Cloud Logging.
5. Automate Security Processes
Automation reduces human error and enhances efficiency. Consider automating:
Vulnerability scanning and patch management.
Incident detection and response workflows.
Configuration compliance checks using Infrastructure as Code (IaC).
6. Secure APIs and Interfaces
APIs are often the weakest link in cloud security. Strengthen them by:
Implementing API gateways to control and monitor API traffic.
Enforcing secure authentication mechanisms like OAuth 2.0.
Regularly testing APIs for vulnerabilities using penetration testing tools.
7. Adopt a Zero Trust Architecture
Zero Trust is a security model that assumes no entity—inside or outside the network—is trustworthy by default. Implementing Zero Trust involves:
Verifying users and devices before granting access.
Segmenting networks to limit lateral movement of attackers.
Continuously monitoring user behavior to detect anomalies.
8. Conduct Regular Security Audits
Routine audits help identify vulnerabilities and ensure compliance. Focus on:
Assessing security configurations for each cloud provider.
Testing backup and disaster recovery plans.
Reviewing access logs and permissions.
9. Educate and Train Employees
Human error is a leading cause of security breaches. Enhance security awareness by:
Conducting regular training on cloud security best practices.
Simulating phishing attacks to educate employees on recognizing threats.
Encouraging a culture of security awareness within the organization.
10. Engage Third-Party Security Solutions
Third-party tools can enhance native cloud security capabilities. Consider solutions for:
Advanced threat detection.
Real-time vulnerability management.
Automated compliance reporting.
Conclusion
Securing multi-cloud environments is a complex but essential task for modern businesses in order to achieve comprehensive cloud security. By implementing these best practices, organizations can mitigate risks, ensure compliance, and maximize the benefits of multi-cloud strategies. Remember, the key to effective multi-cloud security lies in a proactive approach, leveraging the right tools, and fostering a culture of continuous improvement.
Final Thoughts
The dynamic nature of cloud technology requires organizations to stay vigilant and adaptive. As cyber threats evolve, so must your security measures. By prioritizing security in your multi-cloud strategy, you can confidently embrace the opportunities of the cloud while safeguarding your critical assets.
Why Businesses Trust SecureMyOrg for Comprehensive Network Security
At SecureMyOrg, we uncover and fix all possible security vulnerabilities of mobile and web, while providing solutions to mitigate risks. We are trusted by renowned companies like Yahoo, Gojek and Rippling, and with 100% client satisfaction, you’re in safe hands!







Some of the things people reach out to us for –
- Building their cybersecurity program from scratch – setting up cloud security using cost-effective tools, SIEM for alert monitoring, building policies for the company
- Vulnerability Assessment and Penetration Testing ( VAPT ) – We have certified professionals, with certifications like OSCP, CREST – CPSA & CRT, CKA and CKS
- DevSecOps consulting
- Red Teaming activity
- Regular security audits, before product release
- Full time security engineers.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.
