CVE-2024-10914: Overview on the Vulnerability
A critical security vulnerability has been identified in specific D-LINK NAS devices, This flaw impacts devices up to October 8, 2024, the command injection vulnerability in D-Link network-attached storage (NAS) devices puts over 61,000 internet-connected units at risk of exploitation. highlighting the need for immediate attention and mitigation.
The vulnerability resides in the cgi_user_add function found within the cgi_bin/accountmgr.ci_cgi_useradd file. By carefully crafting and manipulating specific data inputs, attackers can exploit this function to execute remote command injection. This flaw enables the execution of arbitrary operating system commands, potentially compromising the entire device and any connected networks.
While the complexity of this exploit is high, requiring advanced technical knowledge to execute, a public exploit has already been released. This significantly increases the risk for users, as it lowers the barrier for exploitation, turning this flaw into a serious threat for unpatched devices.
What are Arbitrary Operating System Commands?
Arbitrary operating system commands refer to any command that can be executed on an operating system, typically at the command-line interface (CLI). These commands are not predefined or limited in scope but rather allow users—or attackers in a security context—to execute any instruction supported by the OS.
In the context of a vulnerability, this means an attacker can:
- Execute System Utilities: Run built-in OS commands like
ls,cd,rm(Linux) ordir,del(Windows) to navigate the filesystem, delete files, or modify directories. - Modify System Configurations: Change user permissions, network settings, or configurations critical to the system’s operation.
- Access Sensitive Data: View, copy, or transfer confidential files stored on the system.
- Install Malicious Software: Download and execute malware or backdoor programs for persistent access.
- Control the Device: Take complete control by creating new user accounts, disabling security mechanisms, or shutting down the device.
Why It’s Dangerous
When an attacker gains the ability to run arbitrary OS commands, they can exploit the full power of the operating system. This allows them to bypass authentication, compromise data integrity, and even use the system as a launch point for further attacks on connected devices. This is why vulnerabilities enabling arbitrary command execution are classified as critical.
Affected D-Link NAS Devices
- DNS 320
- DNS 320 LW
- DNS 325
- DNS 340 L
How Can The Vulnerability Be Exploited?
To exploit this vulnerability, an attacker can send a specifically crafted HTTP GET request to the NAS device, embedding malicious input within the name parameter. Below is an example of such an exploit request:
curl "http://[Target-IP]/cgi-bin/account_mgr.cgi?cmd=cgi_user_add&name=%27;;%27" This curl request constructs a URL that triggers the cgi_user_add command with a name parameter that includes an injected shell command.
Actual Result
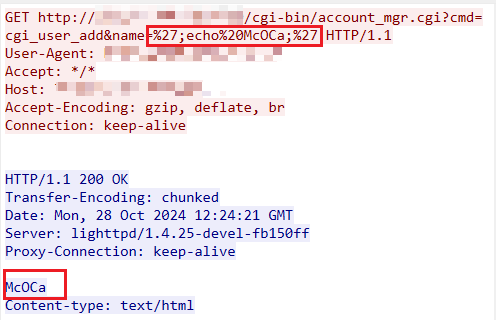
-reference- netsecfish.notion.site
Recommended Fixes
- Firmware Updates: Immediately check for and apply any firmware updates released by D-LINK for the affected models.
- Network Segmentation: Isolate NAS devices from critical systems to limit the impact of any potential breach.
- Monitoring and Logging: Enable logging to detect unusual activity indicative of exploitation attempts.
- Restrict Access: Limit device access to trusted users and IP addresses.
- Disable Unnecessary Features: If possible, disable or restrict the use of the affected
cgi_user_addfunction until a fix is applied.
Conclusion
The command injection vulnerability in D-Link NAS devices poses a significant security risk, especially given the availability of a public exploit. While the complexity of the attack may limit immediate exploitation, the critical nature of the flaw, coupled with the widespread use of these devices, demands urgent action. Applying firmware updates, restricting access, and monitoring for suspicious activity are essential steps to protect your NAS devices and prevent unauthorized access. Proactive measures today can mitigate potential breaches and safeguard sensitive data stored on these systems.
References
About SecureMyOrg
At SecureMyOrg, we uncover and fix all possible security vulnerabilities of mobile and web, while providing solutions to mitigate risks. We are trusted by renowned companies like Yahoo, Gojek and Rippling, and with 100% client satisfaction, you’re in safe hands!
Some of the things people reach out to us for –
- Building their cybersecurity program from scratch – setting up cloud security using cost-effective tools, SIEM for alert monitoring, building policies for the company
- Vulnerability Assessment and Penetration Testing ( VAPT ) – We have certified professionals, with certifications like OSCP, CREST – CPSA & CRT, CKA and CKS
- DevSecOps consulting
- Red Teaming activity
- Regular security audits, before product release
- Full time security engineers.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.