In this blog we will see a step-by-step guide of what goes behind a successful pentest. This not only includes the technical aspects but also the business and legal aspects of it.
If you’re tasked with the responsibility for getting your organisation’s app or website’s pentest done, this blog would definitely help you navigate the waters easily.
Table of Contents
What is a Pentest ?

Pentest also known as Pentesting, a term used interchangeably with Vulnerability Assessment and Penetration Testing ( VAPT ).
A penetration test, colloquially known as a pentest or ethical hacking, is an authorized simulated cyberattack on a computer system, performed to evaluate the security of the system; this is not to be confused with a vulnerability assessment.
– Wikipedia
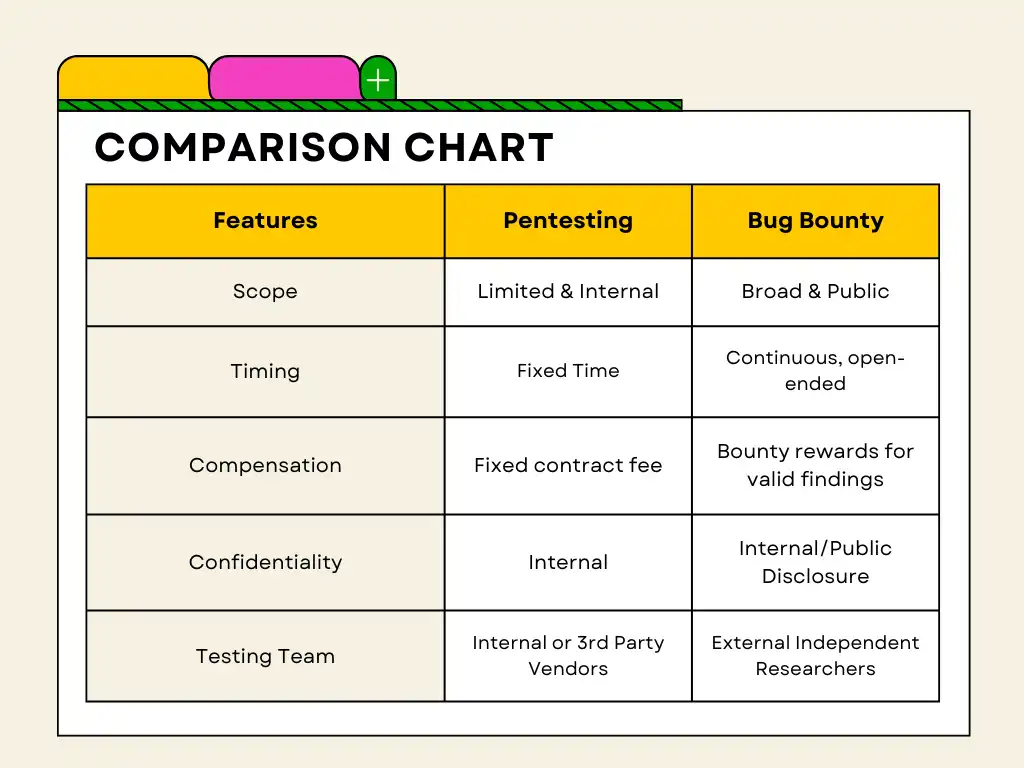
So essentially it’s cracking into computer systems to which you’ve the permissions to do so. If you’re familiar with bug bounty, then you might ask, then what’s the difference between bug bounty and pentest ?
Bug Bounty vs Pentest
Bug Bounty is when organisations have put in a reward aka ‘bounty’ for finding bugs onto one of their systems aka ‘assets’, could be web application, application executable etc. In this case the organisations lay down a set of rules for anyone testing their assets and the corresponding payout ranges for the same. This usually runs for long period of time.
Why do we need a Pentest ?
- Identify Vulnerabilities: Pentests help uncover weaknesses in your systems, applications, and networks that could be exploited by attackers.
- Risk Mitigation: By identifying vulnerabilities early, you can proactively address them, reducing the risk of security breaches and their associated impacts.
- Compliance Requirements: Many industries have regulatory requirements mandating regular security testing, including Pentests, to ensure data protection and compliance.
- Protect customer’s data: Pentests are also done to avoid risking customer’s data to a breach. Pentests help identify security loopholes that can be identified by the attackers to leak sensitive customer data.
- Protect Reputation: Detecting and fixing vulnerabilities before they are exploited helps maintain customer trust and protects your organization’s reputation.
- Continuous Improvement: Pentests provide valuable insights into your security posture, enabling you to continually improve your defenses and stay ahead of emerging threats.
Steps of a Pentest
From the discovery call to the final report submission post retest, there are multiple steps involved, that we take while doing a pentest. These steps ensure a good experience for our clients and increased faith in our testing methodologies. Lets see the steps involved in a pentest ―
- Discovery Call
- Complete Formalities
- Technical Setup
- Day 0
- Daily Updates
- Preliminary Report Submission
- Retest
- Final Report Submission
Deep Dive into the Pentest Process
Let’s elaborate a bit on each of these steps.
Considerations to bear in mind when undergoing a pentest for your organization
- Know your Pentesters – This should be done in the
Discovery Call. Have a chat with them and talk with them about their methodology and their expertise in testing applications from different types of industries such as fintech, edtech etc. - Inform Internally – Before starting the pentest, make sure to keep the infra team and the backend team in the loop. This helps in avoiding unnecessary surprises and promotes smooth and timely testing.
- The Point of Contact – Should be someone who’s more security initiated, ideally a security engineer.
- Staging Environment – Pentesting should be done on a close replica of your prod environment and not on the prod environment. Many times companies dont have parity between staging and production environment, hence they conduct vapt on prod. This should be avoided.
- Identifying Testing Traffic – Ask the agency to add a unique header in all the requests they’re sending to your machines. This helps in avoiding unnecessary alert fatigue, as those testing payloads might trigger a lot of internal systems and alarms.
- What’s Left Out – Not only ask for what’s tested for but also make sure to get updated with whatever is left out and why.
- Video Proof of Concept – Prefer video proof of concepts for easy replication.
- Preliminary Report Submission – Post the preliminary report submission, make sure to apprise the DevOps and backend team.
Important things in a Pentest
Setting Clear Expectations
Make sure to properly document your expectations in the SoW.Clear and Prompt Communication
Keep your client updated of your work. They shouldn’t feel that you aren’t working on the pentest.- Apprise them of any critical findings, ASAP.
- Let them know, if you’ll be load testing their systems.
Accountability
We maintain this by submitting a daily report of endpoints tested and test cases on our slack channel.
In the end of the pentest, we also submit the full log of our BURP endpoints tested and coverage to ensure accountability and transparency.Timeliness
Make sure to give the deliverables on time. There could be exploits that would be taking much time to exploit, in cases where there’s a delay inform the client accordingly.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.