John the Ripper stands out as a versatile and powerful password recovery tool. Designed to identify weak passwords, it serves as a vital resource for penetration testers, security analysts, and ethical hackers aiming to bolster system security. This guide delves into the essential tips and tricks to master John the Ripper and use it effectively in ethical hacking endeavors.
Table of Contents
Understanding John the Ripper
John the Ripper, often referred to simply as “John,” is an open-source password-cracking tool developed by Openwall. It is known for its versatility and support for a wide range of password hash types, including:
Unix/Linux-based hashes (e.g., DES, MD5, SHA-512)
Windows LM and NTLM hashes
Password-protected archives (e.g., ZIP, RAR)
Database hashes (e.g., MySQL, Oracle)
John the Ripper’s multi-platform compatibility and extensive feature set make it indispensable for ethical hacking and security auditing.
Setting Up John the Ripper
John the Ripper is available in two versions:
Core Version: The basic release suitable for general use.
Jumbo Version: A community-enhanced version with additional features and support for more hash types.
The recommended version for ethical hackers is the Jumbo version, which can be downloaded from the official website.
Step 2: Installation
Installation procedures vary by operating system. Below is a general guide:
On Unix/Linux:
cmd
sudo apt-get update
sudo apt-get install john From Source:
git clone https://github.com/openwall/john -b bleeding-jumbo john-jumbo
cd john-jumbo/src
./configure && make -s clean && make -sj4 On Windows:
Download the binary package and extract it to a directory, then add it to your system’s PATH.
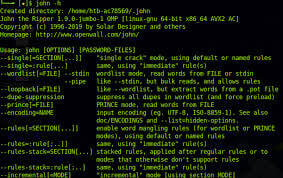
Step 3: Verify Installation
Run the following command to verify the installation:
john --test This ensures all components are functioning correctly.
Key Features of John the Ripper
John the Ripper provides various cracking modes, each tailored to specific scenarios:
Single Crack Mode: Focuses on simple passwords derived from usernames.
Wordlist Mode: Uses a predefined wordlist to match passwords.
Incremental Mode: Performs a brute-force attack by generating every possible combination.
External Mode: Allows the use of custom scripts for advanced cracking strategies.
How to Use John the Ripper
Step 1: Prepare the Input
Before cracking passwords, you need the hashed password file. Ethical hackers typically retrieve these files from target systems after obtaining proper authorization.
For example, extract hashes from a Linux shadow file:
unshadow /etc/passwd /etc/shadow > hashes.txt Step 2: Select a Cracking Mode
There are two main cracking modes: The Wordlist mode and the Incremental mode. Choose the appropriate mode based on your goal:Wordlist Mode:
cmd
john --wordlist=rockyou.txt hashes.txt Explanation: Wordlist mode leverages a predefined list of potential passwords. This mode is effective when common or reused passwords are likely. By comparing each entry in the wordlist against the hashes, John the Ripper can identify matches efficiently.
Incremental Mode:
john --incremental hashes.txt Explanation: Incremental mode performs a brute-force attack, systematically generating every possible combination of characters within a defined set. This mode is powerful but time-intensive, often used when other approaches fail or when the password is highly complex and unpredictable.
Show Cracked Passwords:
Once the process is complete, display the cracked passwords:
cmd
john --show hashes.txt
Using John the Ripper: Advanced Tips and Tricks
1. Custom Wordlists
Tailor your wordlists to match the target’s environment. Use tools like Crunch to generate wordlists with specific patterns:
cmd
crunch 8 12 abcdefgh123 > custom_wordlist.txtThis creates a wordlist of passwords 8 to 12 characters long, using specified characters.
2. Rule-Based Cracking
John the Ripper supports custom rules for modifying wordlists to simulate real-world password variations. Enable rules with:
crunch john --wordlist=rockyou.txt --rules hashes.txtRules can append numbers, change cases, or substitute characters.
3. Parallel Processing
Speed up cracking by leveraging multiple CPU cores. Use the --fork option:
crunch john --wordlist=rockyou.txt --fork=4 hashes.txtThis splits the workload across four processes, reducing overall runtime.
4. Resume Interrupted Sessions
Long-running cracking sessions can be paused and resumed using session management:
To start a session:
john --session=my_session --wordlist=rockyou.txt hashes.txtTo resume:
john --restore=my_session5. Optimize Hash Format
Explicitly specify the hash format for better performance. For example:
john --format=nt hashes.txt
This targets NTLM hashes specifically.
6. GPU Acceleration
For complex hashes, GPU acceleration can dramatically improve performance. Tools like Hashcat may complement John the Ripper for GPU-based cracking.
Mastering John The Ripper: Ethical Considerations
As a powerful tool, John the Ripper must be used responsibly. Always adhere to the following ethical guidelines to ensure your work aligns with the principles of ethical hacking and cybersecurity:
1. Obtain Explicit Permission
Before using John the Ripper, secure clear and documented permission from the system owner or client. Unauthorized use of the tool, even with good intentions, can lead to severe legal and ethical consequences.
2. Maintain Confidentiality
Any passwords or sensitive information uncovered during ethical hacking must be handled with the utmost confidentiality. Share findings only with authorized individuals and avoid storing sensitive data longer than necessary.
3. Educate and Protect
Use the insights gained from password audits to educate users about creating strong, secure passwords. Highlight the importance of using password managers and two-factor authentication (2FA) for enhanced security.
4. Stay Within Legal Boundaries
Understand and comply with local and international laws regarding cybersecurity and ethical hacking. Unauthorized password cracking is illegal and can damage your professional reputation.
5. Use Results Constructively
The primary goal of using John the Ripper should be to strengthen security defenses. Report vulnerabilities to the appropriate parties and assist in implementing stronger password policies.
6. Avoid Misuse
Never use John the Ripper for malicious purposes, such as unauthorized data breaches or personal gain. Ethical hacking requires maintaining the highest standards of integrity.
By adhering to these principles, you can ensure that your use of John the Ripper contributes positively to the security landscape.
Conclusion
Mastering John the Ripper is a valuable skill for ethical hackers, enabling them to identify and mitigate password vulnerabilities. By understanding its features, cracking modes, and advanced techniques, you can effectively incorporate this tool into your cybersecurity toolkit. Remember, with great power comes great responsibility—always use John the Ripper ethically and within legal boundaries to make systems more secure.
References
Why Businesses Trust SecureMyOrg for Comprehensive Network Security
At SecureMyOrg, we uncover and fix all possible security vulnerabilities of mobile and web, while providing solutions to mitigate risks. We are trusted by renowned companies like Yahoo, Gojek and Rippling, and with 100% client satisfaction, you’re in safe hands!







Some of the things people reach out to us for –
- Building their cybersecurity program from scratch – setting up cloud security using cost-effective tools, SIEM for alert monitoring, building policies for the company
- Vulnerability Assessment and Penetration Testing ( VAPT ) – We have certified professionals, with certifications like OSCP, CREST – CPSA & CRT, CKA and CKS
- DevSecOps consulting
- Red Teaming activity
- Regular security audits, before product release
- Full time security engineers.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.