As businesses continue to evolve, so do their data management needs. Multi-cloud data management has emerged as a strategic solution for organizations seeking to leverage multiple cloud providers for storing, processing, and managing data. This blog explores the advantages, challenges, and best strategies for implementing multi-cloud data management effectively.
Understanding Multi-Cloud Data Management
Multi-cloud data management refers to the practice of using multiple cloud platforms—such as AWS, Azure, and Google Cloud—to store and manage an organization’s data. Unlike single-cloud or hybrid-cloud solutions, a multi-cloud strategy spreads resources across several platforms, reducing dependency on a single provider and enhancing flexibility.
As businesses generate unprecedented amounts of data, the need for agile, secure, and efficient management solutions has never been greater. Multi-cloud strategies aim to address these demands while offering resilience and competitive advantages.
Pros of Multi-Cloud Data Management
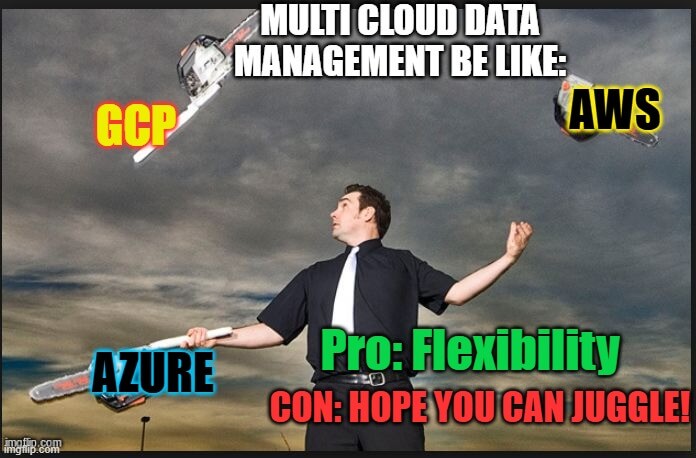
1. Avoiding Vendor Lock-In
One of the most significant advantages of a multi-cloud approach is the ability to avoid vendor lock-in. Relying on a single provider can limit flexibility and make switching costly or complex. Multi-cloud strategies give businesses the freedom to choose the best provider for specific tasks.
2. Increased Resilience and Redundancy
By distributing data and applications across multiple cloud platforms, organizations can enhance their resilience. If one provider experiences downtime, the others can maintain operations, ensuring business continuity.
3. Optimized Costs
Different providers offer varying pricing models and features. A multi-cloud strategy enables businesses to choose cost-effective solutions tailored to their specific needs, optimizing resource allocation and reducing overall expenses.
4. Enhanced Performance
Using multiple providers allows businesses to place workloads closer to end-users, reducing latency and improving application performance. Geographic flexibility ensures that data and services are accessible globally.
5. Regulatory Compliance
For organizations operating in multiple regions, a multi-cloud strategy makes it easier to comply with local data sovereignty laws. Data can be stored within specific jurisdictions as required by regulations such as GDPR or CCPA.
Cons of Multi-Cloud Data Management
1. Increased Complexity
Managing multiple cloud environments can be complex. Each provider has unique interfaces, policies, and tools, making integration and oversight challenging.
2. Security Risks
While multi-cloud setups can enhance resilience, they also expand the attack surface. Ensuring consistent security across all platforms requires robust policies and tools.
3. Data Transfer Costs
Moving data between different cloud platforms can incur significant transfer fees. Without careful planning, these costs can escalate quickly.
4. Skillset Requirements
Operating multiple cloud platforms necessitates a diverse skill set. Organizations may need to invest in training or hire specialized personnel to manage their multi-cloud environments effectively.
5. Lack of Unified Visibility
Without the right tools, monitoring and managing data across different platforms can result in silos. This lack of unified visibility can hinder decision-making and operational efficiency.
Strategies for Effective Multi-Cloud Data Management
1. Establish Clear Objectives
Before implementing a multi-cloud strategy, define your objectives. Are you looking to improve performance, reduce costs, or enhance resilience? Clear goals will guide your decisions and ensure alignment with business needs.
2. Invest in Cloud Management Tools
Cloud management platforms (CMPs) simplify the oversight of multi-cloud environments. These tools provide unified dashboards, performance monitoring, and cost analysis, helping businesses maintain control.
3. Prioritize Security and Compliance
Develop a comprehensive security strategy that spans all cloud platforms. This includes:
Encryption: Protect data at rest and in transit.
Access Controls: Implement role-based access and multi-factor authentication.
Compliance Automation: Use tools to track and report regulatory adherence.
4. Optimize Workload Distribution
Distribute workloads strategically across providers based on their strengths. For example:
Use AWS for scalable storage.
Leverage Google Cloud for advanced analytics.
Utilize Azure for enterprise-grade applications. This approach maximizes performance and minimizes costs.
5. Monitor Costs Continuously
Regularly review your spending across all platforms. Identify underutilized resources and eliminate waste. Tools like AWS Cost Explorer, Azure Cost Management, or third-party solutions can help optimize expenditures.
6. Simplify Integration
Use APIs and middleware to ensure seamless integration between cloud platforms. This reduces complexity and ensures data flows smoothly across environments.
7. Train Your Team
Invest in training programs to upskill your IT team. Certifications in AWS, Azure, and Google Cloud can enhance expertise and ensure effective management of multi-cloud environments.
8. Develop a Disaster Recovery Plan
Ensure your multi-cloud strategy includes robust disaster recovery protocols. Regularly back up data across platforms and test recovery processes to minimize downtime during disruptions.
Conclusion: Embracing the Future with Multi-Cloud
Multi-cloud data management offers a powerful solution for organizations navigating the complexities of modern data needs. While it comes with challenges like complexity and security risks, the benefits of flexibility, resilience, and cost optimization make it a compelling choice.
By establishing clear objectives, investing in the right tools, and implementing robust strategies, businesses can revolutionize data protection unlock the full potential of multi-cloud environments. As technology evolves, a well-executed multi-cloud strategy will be key to staying competitive and future-ready.
Why Businesses Trust SecureMyOrg for Comprehensive Network Security
At SecureMyOrg, we uncover and fix all possible security vulnerabilities of mobile and web, while providing solutions to mitigate risks. We are trusted by renowned companies like Yahoo, Gojek and Rippling, and with 100% client satisfaction, you’re in safe hands!







Some of the things people reach out to us for –
- Building their cybersecurity program from scratch – setting up cloud security using cost-effective tools, SIEM for alert monitoring, building policies for the company
- Vulnerability Assessment and Penetration Testing ( VAPT ) – We have certified professionals, with certifications like OSCP, CREST – CPSA & CRT, CKA and CKS
- DevSecOps consulting
- Red Teaming activity
- Regular security audits, before product release
- Full time security engineers.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.