Network penetration testing has emerged as a powerful tool to secure digital infrastructures. With businesses increasingly reliant on interconnected networks, understanding and addressing security gaps has never been more crucial. This blog dives deep into network penetration testing, exploring its essence, methodologies, and significance in safeguarding against cyber threats.
Table of Contents
Introduction to Network Penetration Testing

Network penetration testing, often abbreviated as pen testing, is a simulated attack on an organization’s network designed to identify vulnerabilities before malicious hackers exploit them. This proactive approach tests the robustness of a network’s defenses, providing actionable insights to enhance security.
The primary goals of network penetration testing include:
- Identifying security weaknesses.
- Validating the effectiveness of existing defenses.
- Enhancing the overall security posture.
In essence, network pen testing is the cybersecurity equivalent of a “fire drill,” ensuring readiness against real-world threats.

How is Network Penetration Testing Done?
In simplest terms, network pen testing works by simulating a real-life attack, providing critical information about potential weaknesses hackers could use as entry points to gain access to your network(s).
Phases of Network Penetration Testing
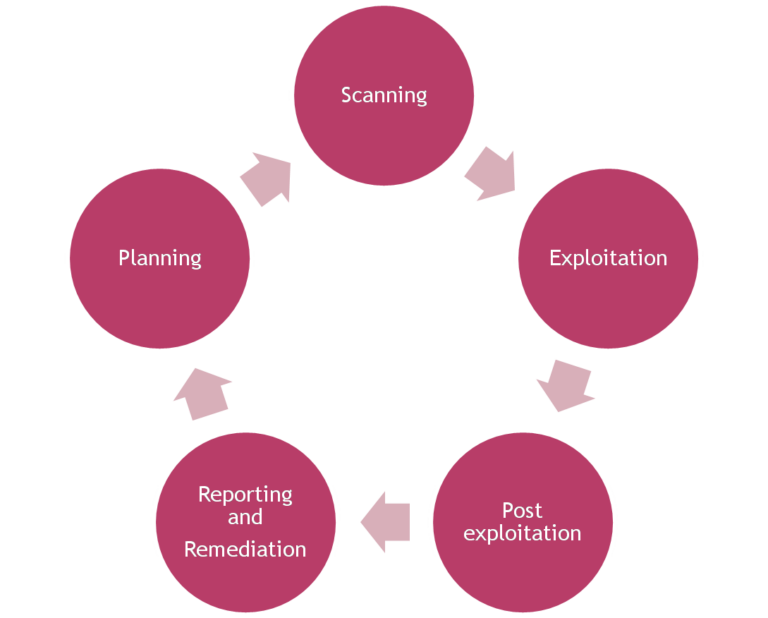
Penetration testing is a structured process consisting of five critical phases:
1. Planning
Before diving into testing, a clear roadmap is essential. This phase involves:
- Defining the scope, objectives, and rules of engagement.
- Collecting information on the network using Open Source Intelligence (OSINT) tools like Shodan and Recon-ng.
2. Scanning
In this phase, testers probe the network to identify:
- Live hosts, open ports, and running services.
- Potential vulnerabilities using tools like Nmap and Nessus. The data collected here forms the blueprint for the testing process.
3. Exploitation
This is where the “action” happens. Testers attempt to exploit vulnerabilities to:
- Gain unauthorized access.
- Test the effectiveness of firewalls, intrusion detection systems, and other defenses. Popular tools include Metasploit and Burp Suite.
4. Post-Exploitation
After gaining access, testers evaluate the potential damage by:
- Moving laterally within the network.
- Simulating data exfiltration and privilege escalation.
5. Reporting and Remediation
The final phase involves creating a detailed report that includes:
- A summary of findings.
- Risk levels associated with identified vulnerabilities.
- Recommendations for mitigation and strengthening defenses.
Common Techniques and Tools in Network Penetration Testing
A range of sophisticated tools and techniques are used in pen testing. These include:
- Reconnaissance Tools: Nmap for network mapping and Wireshark for traffic analysis.
- Vulnerability Scanners: Nessus and OpenVAS for automated vulnerability detection.
- Exploitation Frameworks: Metasploit for developing and testing exploits.
- Password Testing Tools: John the Ripper and Hydra for brute force attacks.
Each tool has its strengths, and testers often use them in combination to cover the entire spectrum of network vulnerabilities.
The Importance of Regular Network Penetration Testing
Why should businesses invest in regular network pen testing?
- Proactive Risk Management: Identifying vulnerabilities before attackers exploit them minimizes risks.
- Compliance and Regulatory Requirements: Many standards, such as GDPR and PCI DSS, mandate regular testing.
- Building Stakeholder Trust: Demonstrating a strong security posture enhances customer and partner confidence.
- Continuous Improvement: Pen tests help organizations evolve their defenses to stay ahead of emerging threats.
Why Businesses Trust SecureMyOrg for Comprehensive Network Security
At SecureMyOrg, we uncover and fix all possible security vulnerabilities of mobile and web, while providing solutions to mitigate risks. We are trusted by renowned companies like Yahoo, Gojek and Rippling, and with 100% client satisfaction, you’re in safe hands!





Some of the things people reach out to us for –
- Building their cybersecurity program from scratch – setting up cloud security using cost-effective tools, SIEM for alert monitoring, building policies for the company
- Vulnerability Assessment and Penetration Testing ( VAPT ) – We have certified professionals, with certifications like OSCP, CREST – CPSA & CRT, CKA and CKS
- DevSecOps consulting
- Red Teaming activity
- Regular security audits, before product release
- Full time security engineers.
Conclusion
Network penetration testing is a cornerstone of modern cybersecurity practices. By uncovering vulnerabilities and providing actionable recommendations, it empowers organizations to safeguard their networks against increasingly sophisticated cyber threats. Whether you’re a small business or a large enterprise, regular pen testing is not a luxury—it’s a necessity.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.
