Web applications form the backbone of many modern businesses, handling everything from customer interactions to financial transactions. However, with their growth, they have also become prime targets for cyberattacks. Web Application Penetration Testing (WAPT) is a vital process that ensures these applications are robust against malicious threats. In this blog, we look into the essence of WAPT, its methodology, and why it is indispensable for cybersecurity.
What is Web Application Penetration Testing?

Web Application Penetration Testing is a simulated cyberattack against a web application to uncover vulnerabilities that could be exploited by attackers. Unlike automated vulnerability scans, penetration testing involves manual and automated techniques to emulate real-world hacking scenarios, making it a more comprehensive approach to identifying security gaps.
What is it’s purpose?
- Proactive Risk Mitigation: Identifies vulnerabilities before attackers can exploit them.
- Compliance: Many regulations, such as GDPR, PCI DSS, and HIPAA, require regular penetration testing.
- Reputation Protection: A secure application ensures customer trust and protects your brand from the fallout of a breach.
It’s general purpose is to determine if a web application system is secure and identify vulnerabilities that could compromise it.
Common Vulnerabilities Found in Web Applications

Understanding potential vulnerabilities is the first step toward securing web applications. The OWASP Top 10 is a gold standard for highlighting the most critical vulnerabilities. Here are some common ones:
- Injection Attacks:
- Examples: SQL injection, Command injection.
- Impact: Data theft, unauthorized access.
- Cross-Site Scripting (XSS):
- Types: Stored, Reflected, DOM-based.
- Impact: Session hijacking, malware injection.
- Broken Authentication:
- Weak login mechanisms can lead to unauthorized access.
- Sensitive Data Exposure:
- Inadequate encryption can expose sensitive information such as passwords and payment details.
- Security Misconfigurations:
- Unpatched servers, unnecessary features enabled, or improper error messages can leak critical information.
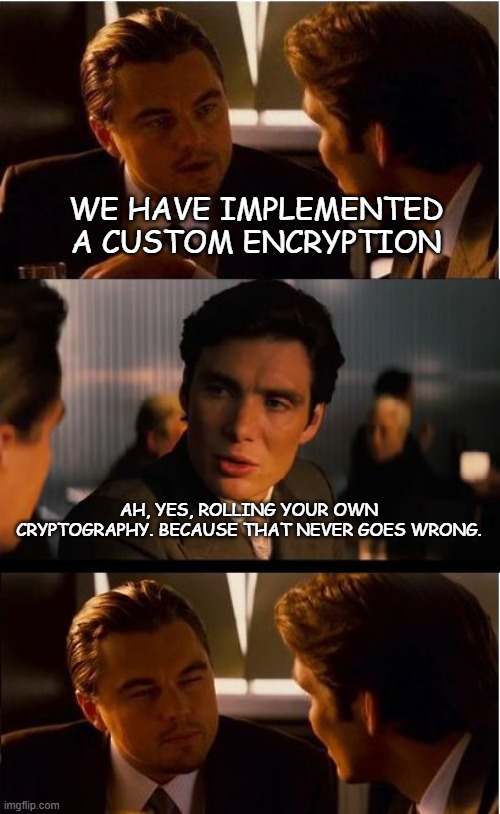
- Weak encryption algorithms:
- Without using tested standards like AES, homebrewed encryption is often trivial as custom encryption often leads to insecure practices, like hardcoding keys in the source code. This is a gift to attackers if the code is exposed.
A structured approach is key to effective penetration testing. Below are the main phases:
1. Planning and Reconnaissance
- Goal: Understand the application and its environment.
- Activities:
- Gather intelligence using tools like Shodan or Google Dorking.
- Map the application’s architecture and endpoints.
2. Scanning and Enumeration
- Goal: Identify potential vulnerabilities.
- Techniques:
- Use tools like Nmap for port scanning.
- Employ Burp Suite or OWASP ZAP to analyze application traffic and locate weaknesses.
3. Exploitation
- Goal: Test the identified vulnerabilities by attempting exploitation.
- Examples:
- Exploiting an XSS vulnerability to execute arbitrary scripts.
- Bypassing authentication mechanisms using session replay attacks.
4. Post-Exploitation
- Goal: Assess the impact of a successful attack.
- Activities:
- Explore data access and system control capabilities gained.
- Identify any lateral movement opportunities.
5. Reporting
- Goal: Document findings and recommendations.
- Contents:
- List of vulnerabilities discovered.
- Proof of concept (POC) for each exploit.
- Recommendations for mitigation and prevention.
Common Tools Used for Web Application Penetration Testing
Several tools aid penetration testers in automating and streamlining tasks. Some of the most popular ones include:
- Burp Suite: A comprehensive suite for intercepting and manipulating web traffic.
- OWASP ZAP: A free alternative to Burp Suite with robust scanning capabilities.
- Nikto: A web server scanner that identifies dangerous files, outdated software, and other issues.
- SQLmap: Automates SQL injection attacks and database enumeration.
- Metasploit: A framework for developing and executing exploit code against a remote target.
The right combination of tools can make all the difference in uncovering critical vulnerabilities. However, effective penetration testing also requires addressing challenges like false positives and complex environments, below are some of the challenges in web application penetration testing.
Challenges in Web Application Penetration Testing
- Complex Applications: Modern applications use frameworks, APIs, and microservices, increasing the testing surface.
- Time Constraints: Limited time to test large applications comprehensively.
- False Positives/Negatives: Ensuring accuracy in detecting and prioritizing vulnerabilities.
- Legal and Ethical Considerations: Ensuring all testing activities are authorized and comply with local laws.
Navigating these challenges requires not only technical expertise but also strategic planning. Up next, we’ll delve into best practices that can help streamline the penetration testing process.
Best Practices for Effective Penetration Testing
To maximize the effectiveness of penetration testing, adhere to these best practices:
- Define Clear Objectives: Align the scope of the test with business goals.
- Use a Combination of Manual and Automated Testing: Automated tools are efficient, but manual testing uncovers complex vulnerabilities.
- Stay Updated: Threat landscapes evolve; ensure tools and methods are up-to-date.
- Collaborate with Development Teams: Work closely with developers to fix identified vulnerabilities.
- Regular Testing: Schedule periodic testing to address new vulnerabilities and application changes.
Implementing these best practices not only strengthens your testing process but also ensures lasting security improvements. The next step is understanding the compliance landscape where WAPT plays a critical role.
The Role of WAPT in Compliance
Regulatory compliance is another driving factor behind WAPT. Here’s how it aligns with key standards:
- PCI DSS (Payment Card Industry Data Security Standard):
- Regular penetration tests are mandatory for businesses handling payment data.
- GDPR (General Data Protection Regulation):
- Requires robust data protection measures, which can be validated through testing.
- ISO 27001:
- Encourages regular risk assessments, including penetration testing, as part of an information security management system.
Conclusion
Web Application Penetration Testing is an essential pillar of any robust cybersecurity strategy. By proactively identifying and addressing vulnerabilities, organizations can safeguard sensitive data, comply with regulations, and build customer trust. As web applications grow in complexity and importance, investing in regular and thorough penetration testing is no longer optional—it is a necessity.
Whether you’re a developer, a business owner, or a cybersecurity professional, understanding and implementing WAPT will ensure that your applications are not just functional but also secure against the ever-evolving threat landscape.
References
About SecureMyOrg
At SecureMyOrg, we uncover and fix all possible security vulnerabilities of mobile and web, while providing solutions to mitigate risks. We are trusted by renowned companies like Yahoo, Gojek and Rippling, and with 100% client satisfaction, you’re in safe hands!
Some of the things people reach out to us for –
- Building their cybersecurity program from scratch – setting up cloud security using cost-effective tools, SIEM for alert monitoring, building policies for the company
- Vulnerability Assessment and Penetration Testing ( VAPT ) – We have certified professionals, with certifications like OSCP, CREST – CPSA & CRT, CKA and CKS
- DevSecOps consulting
- Red Teaming activity
- Regular security audits, before product release
- Full time security engineers.
Relevant Posts

Top Cybersecurity Threats Facing Businesses In 2026
Businesses entering 2026 face a security landscape that is more complex, more interconnected, and far less forgiving than in previous years. Cybersecurity threats no longer

Top 5 Security Weaknesses Cloud-Native Apps Commonly Ignore
Cloud-native applications promise speed, flexibility, and scalability. Teams ship features faster, infrastructure adapts automatically, and operational overhead drops. Yet many organizations discover later that security

Why Weak Serverless Application Security Puts Your Business at Risk
Weak security in serverless environments often goes unnoticed until it leads to real damage. Misconfigured triggers, broad permissions, and poor visibility can expose sensitive data and disrupt business operations. Understanding where the risks appear is the first step toward building safer, more reliable serverless applications.

What Is Penetration Testing as a Service?
Penetration testing as a service (PTaaS) lets experts simulate real attacks to uncover vulnerabilities before hackers do. This guide explains the process, benefits, and costs, helping businesses strengthen defenses with predictable, ongoing security checks.

How To Inspect Encrypted Traffic Without Breaking Privacy
Network administrators face a challenge: securing systems while respecting privacy. This guide explains how to inspect encrypted traffic without breaking privacy using metadata, anomaly detection, and machine learning ensuring visibility, compliance, and trust.

How to Audit Infrastructure as Code (IaC) for Security Vulnerabilities
Discover how to audit Infrastructure as Code (IaC) for security vulnerabilities with this practical guide. Learn to scan IaC files using tools like Checkov, fix issues like exposed resources, and integrate audits into CI/CD pipelines. Protect your cloud systems from misconfigurations and ensure compliance with clear, actionable steps.
